Understanding DKIM to the letter
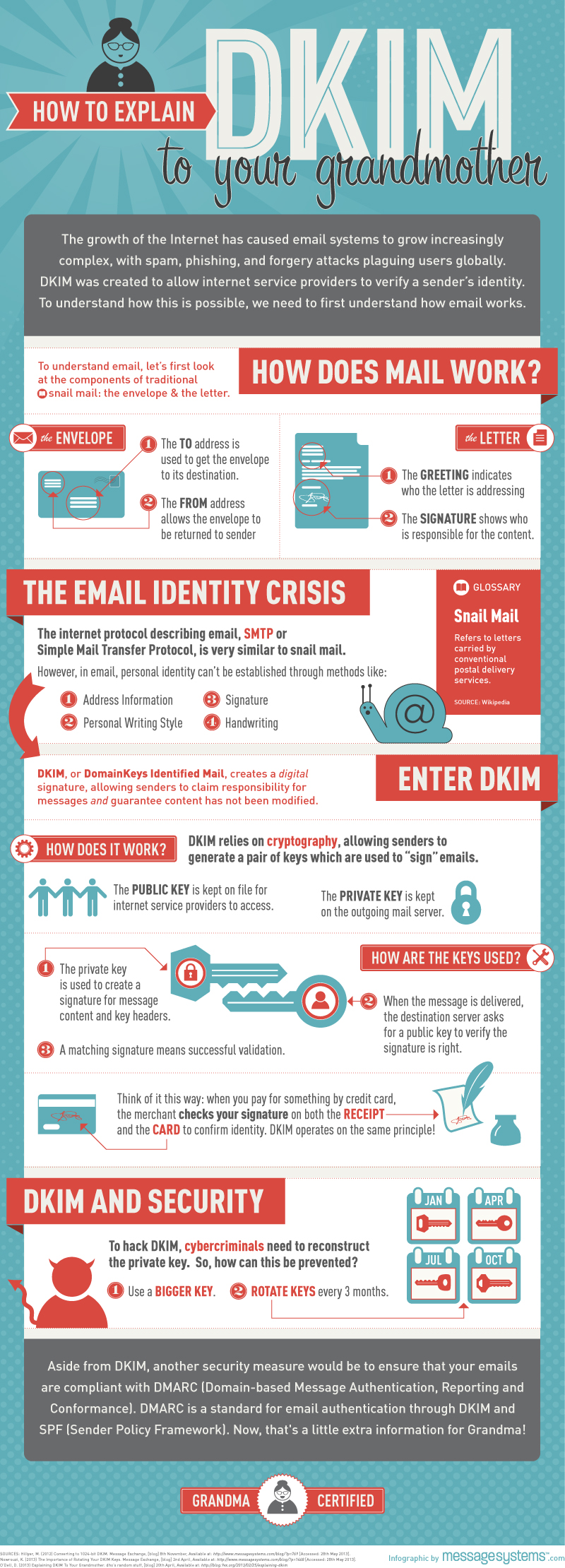
DKIM are the initials for Domainkeys Identified Mail, which is a way in which electronic messages are tied to the sender or an organization with a proof of ownership and non-tempered mails. It mainly works with the current domain in which the email message has been sent from, thus protecting the legitimacy of the mail contents. The main reason why DKIM was introduced to the online market and especially to email messaging was to prevent scams and fraudulent messages send through the same media. Anyone who uses this system has a lesser risk of email impersonation as it helps verify the sender’s details to the recipient easily.
How does DKIM work to protect and verify identity?
You may be wondering how this system works to protect mails and recipients of the same. DKIM works by including a digital signature to each mail being sent over the domain, which then guarantees that the message content has not been tampered with. This works by including a public and private key which creates a digital signature of the sender. When the recipient finally receives the email, he is then required to enter the private key generated through DKIM, and a matching key verifies the source from which the mail came from. If no key is provided, or a wrong one is found, then the viability of the message is almost impossible, meaning the message has either been tampered with, or is a spam. Through this cryptography, one can easily identify spam and legit messages, thus help filter unknown messages.
Benefits
The good thing with using DKIM is that, it is very possible for one to generate a user key and send it to all email contacts to help prevent spam as well as protect contents of the same. By doing this, it helps protect hackers and other malicious persons from intervening or changing the contents of the mail contents, hence securing whatever contents of the same. Nevertheless, although you may be using DKIM to protect messages sent and received, this does not mean that they care hacker proof. Hackers can regenerate the key and open messages especially if the key is simple and predictable. This means you, the user, need to generate a key that is hard to predict, and with DKIM’s help, it is possible to generate long strong keys to use in all sent mails. It is also advisable for you to use different keys randomly each month to help make it harder for hackers to predict.
There are many benefits that come from using DKIM as a security measure on all sent mails. Just like the seal used in ancient days to protect the contents of a letter, the security keys should serve an almost similar function. This security feature is also useful to companies and corporates to help protect unauthorized messages, as well as abuse of the company’s email server. In addition to this, circulation of spam mails online has been a major challenge to many people, but thanks to DKIM, these messages can be filtered never to be seen in your inbox.
Although millions of people visit Brandon's blog each month, his path to success was not easy. Go here to read his incredible story, "From Disabled and $500k in Debt to a Pro Blogger with 5 Million Monthly Visitors." If you want to send Brandon a quick message, then visit his contact page here.
